Cloud is a shared responsibility

Manasi Saha, Owner & Founder, Macaws Infotech
Important factors for cyber security readiness
A cybersecurity readiness presents and discusses fundamental objectives that organizations must achieve in order to consider themselves cybersecurity ready.
Cybersecurity readiness is defined as the state of being able to detect and effectively respond to computer security breaches and intrusions, malware attacks, phishing attacks, theft of data and intellectual property from both outside and inside the network.
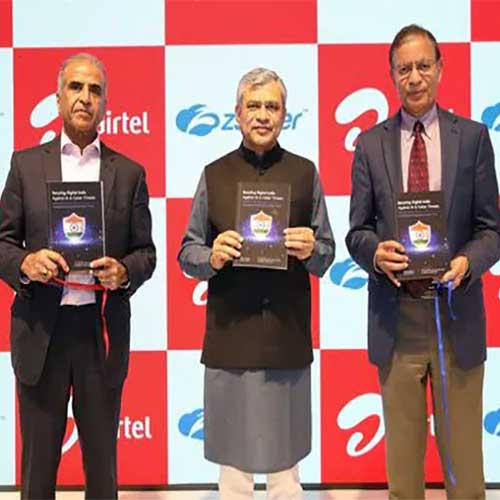
Cybersecurity plan objectives are defined and a timetable, milestones, measures and metrics are established for each of critical components that an organization needs to possess for a high degree of situational awareness into its network operations and network utilization. Without a comprehensive understanding of its most important information assets, how its information systems and networks operate, how its information systems support business operations, and what information is moving in, out and through its networks, an organization cannot achieve cybersecurity readiness. Cloud is a shared responsibility. The organization needs to know that Identity, Infra & Encryption needs to be identified and protected by Cloud security products.
Problems faced by the CIOs/CISOs
The CISO leadership position is primarily responsible for establishing the correct security and data governance practices for a company, and for enabling the capabilities for a scalable, low-risk business operations framework for a company in a constantly-shifting technological environment. A CISO cares about a company’s entire security strategy and all of the complexities therein: protecting against a data breach, meeting industry data compliance regulations, establishing and refining employee management while developing protocols to reduce the human error weaknesses that impact security, disaster recovery and business continuity solutions, documentations, and finessing senior stakeholder management. It’s a big role with an enormous set of challenges.
Commonly adopted technologies
Mobile Technology, Internet of Things (IoT), Robotics, AI & ML, Augmented Reality, Big Data and Real-Time Analytics, Digital Twin, API-Based Integrations etc.
To face the challenges
We need to transform and evolve with new Cybersecurity technologies and compliance, come out of legacy and adopt Next Generation Solutions, move from signature based to signature less, focus more on threat hunting, threat detection and prevention, MDR, ZTNA framework, Cloud Security etc.
See What’s Next in Tech With the Fast Forward Newsletter
Tweets From @varindiamag
Nothing to see here - yet
When they Tweet, their Tweets will show up here.