Vulnerabilities in IoT

An IoT device typically lacks the required built-in security to counter security threats. Common vulnerabilities and exposures allow cyber criminals to breach the device and use it as a foothold to launch sophisticated cyberattacks.
Vulnerability disclosures impacting extended internet of things devices has increased by 57% in the first half of 2022 compared to the previous six months, as per the research by Claroty.
The report also found that over the same time period, vendor self-disclosures increased by 69%, becoming more prolific reporters than independent research outfits for the first time, and fully or partially remediated firmware vulnerabilities increased by 79%, a notable improvement given the relative challenges in patching firmware versus software vulnerabilities.
The report is an examination and analysis of vulnerabilities impacting the Extended Internet of Things, a vast network of cyber-physical systems including operational technology and industrial control systems, Internet of Medical Things, building management systems, and enterprise IoT.
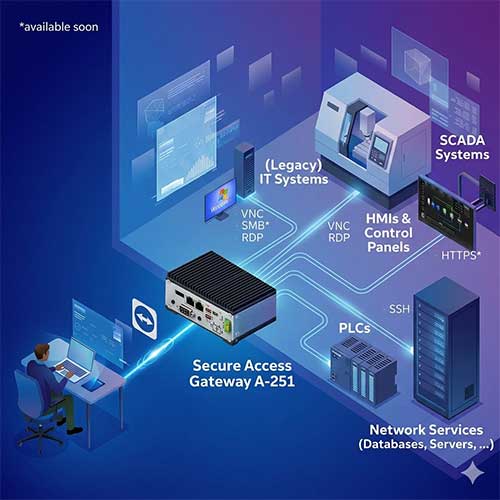
The top mitigation step is network segmentation (recommended in 45% of vulnerability disclosures), followed by secure remote access (38%) and ransomware, phishing, and spam protection (15%).
After decades of connecting things to the internet, cyber-physical systems are having a direct impact on our experiences in the real world, including the food we eat, the water we drink, the elevators we ride, and the medical care we receive,” say experts.
A report says 15% of vulnerabilities were found in IoT devices, a significant increase from 9% in Team82’s last report covering the second half of 2021. Additionally, for the first time, the combination of IoT and IoMT vulnerabilities (18.2%) exceeded IT vulnerabilities (16.5%). This indicates enhanced understanding on the part of vendors and researchers to secure these connected devices as they can be a gateway to deeper network penetration.
The Published firmware vulnerabilities were nearly on par with software vulnerabilities (46% and 48% respectively), a huge jump from the 2H 2021 report when there was almost a 2:1 disparity between software (62%) and firmware (37%).
The Claroty report claims that they had conducted this research to give decision makers within critical sectors a complete snapshot of the XIoT vulnerability landscape, empowering them to properly assess, prioritize, and address risks to the mission-critical systems underpinning public safety, patient health, smart grids and utilities, and more.
See What’s Next in Tech With the Fast Forward Newsletter
Tweets From @varindiamag
Nothing to see here - yet
When they Tweet, their Tweets will show up here.