Hackers Install Secret Backdoor on Thousands of Microsoft SQL Servers
While the whole world is struggling with the Chinese gifted corona virus to the world,at the same time hackers are continuing with the idea of crooks. Cybersecurity researchers uncovered a sustained malicious campaign dating back to May 2018 that targets Windows machines running MS-SQL servers to deploy backdoors and other kinds of malware, including multi-functional remote access tools (RATs) and cryptominer.
Named "Vollgar" after the Vollar cryptocurrency it mines and its offensive "vulgar" modus operandi, researchers at Guardicore Labs said the attack employs password brute-force to breach Microsoft SQL servers with weak credentials exposed to the Internet.
Researchers claim the attackers managed to successfully infect nearly 2,000-3,000 database servers daily over the past few weeks, with potential victims belonging to healthcare, aviation, IT & telecommunications, and higher education sectors across China, India, the US, South Korea, and Turkey.
Vollgar Attack Chain: MS-SQL to System Malware
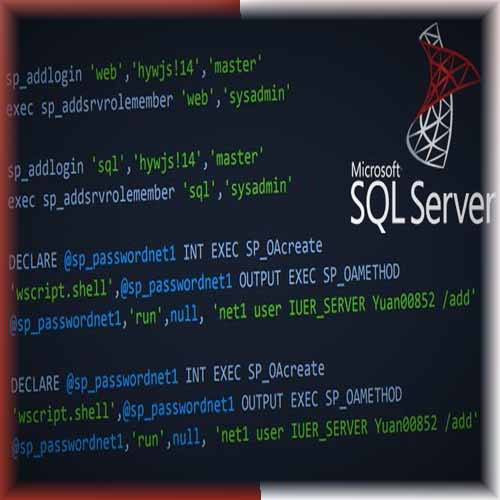
The Vollgar attack starts off with brute-force login attempts on MS-SQL servers, which, when successful, allows the interloper to execute a number of configuration changes to run malicious MS-SQL commands and download malware binaries.
"Attackers [also] validate that certain COM classes are available - WbemScripting.SWbemLocator, Microsoft.Jet.OLEDB.4.0 and Windows Script Host Object Model (wshom). These classes support both WMI scripting and command execution through MS-SQL, which will be later used to download the initial malware binary," the researchers said.
One of the initial payloads, named SQLAGENTIDC.exe or SQLAGENTVDC.exe, first proceeds to kill a long list of processes with the goal of securing the maximum amount of system resources as well as eliminate other threat actors' activity and remove their presence from the infected machine.
Furthermore, it acts as a dropper for different RATs and an XMRig-based crypto-miner that mines Monero and an alt-coin called VDS or Vollar.
Attack Infrastructure Hosted On Compromised Systems
Guardicore said attackers held their entire infrastructure on compromised machines, including its primary command-and-control server located in China, which, ironically, was found compromised by more than one attack group.
Use Strong Passwords to Avoid Brute-Force Attacks
With about half-a-million machines running MS-SQL database service, the campaign is yet another indication that attackers are going after poorly protected database servers in an attempt to siphon sensitive information. It's essential that MS-SQL servers that are exposed to the internet are secured with strong credentials.
"What makes these database servers appealing for attackers apart from their valuable CPU power is the huge amount of data they hold," Guardicore researchers concluded. "These machines possibly store personal information such as usernames, passwords, credit card numbers, etc., which can fall into the attacker's hands with only a simple brute-force."
See What’s Next in Tech With the Fast Forward Newsletter
Tweets From @varindiamag
Nothing to see here - yet
When they Tweet, their Tweets will show up here.