Most organizations assume that encrypted data is secure. However, cybersecurity experts warn that this assumption may not hold true in the future. As quantum computing advances, attackers are already preparing for a time when today’s encryption methods could be broken. Instead of trying to decrypt sensitive information now, many adversaries are collecting encrypted data and storing it so it can be deciphered later once quantum computers become powerful enough.
This tactic is known as “harvest now, decrypt later.” It involves intercepting and storing encrypted communications today with the intention of decrypting them years later when quantum capabilities mature. The strategy poses a significant risk for organizations that handle sensitive data such as financial records, intellectual property, healthcare information, and government communications. Information transmitted securely today could become readable in the future if it relies on encryption standards that quantum computers can eventually defeat.
The challenge lies in the fact that many of the encryption algorithms widely used today—including RSA and elliptic curve cryptography (ECC)—were not designed to withstand the computational power of quantum machines. Once large-scale quantum computers become viable, these algorithms could be broken in a fraction of the time required by classical computing systems. This creates a pressing need for organizations to rethink how they protect sensitive information over the long term.
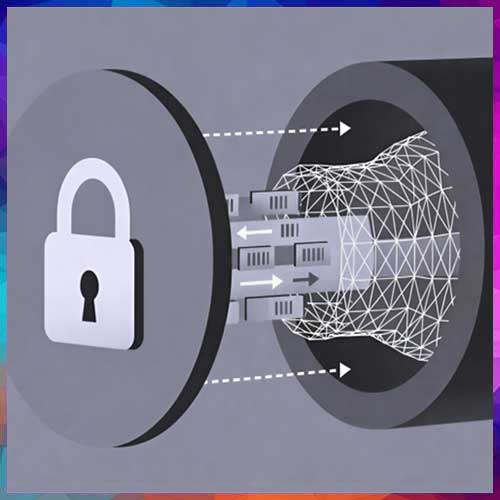
To address this emerging risk, cybersecurity experts are advocating the adoption of post-quantum cryptography (PQC)—a new generation of encryption techniques designed to remain secure even against quantum attacks. PQC algorithms are built to resist the advanced mathematical capabilities that quantum computers will bring, ensuring that encrypted data remains protected in the future.
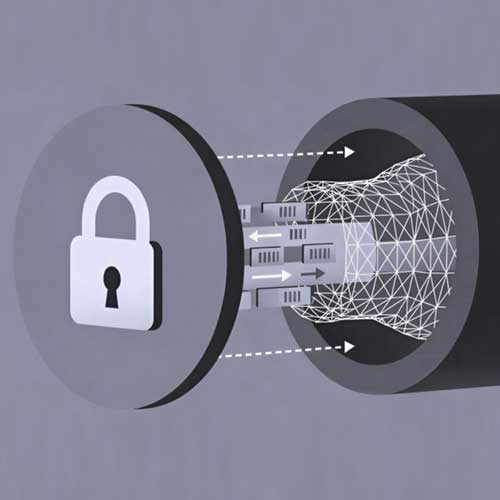
One practical approach gaining momentum is hybrid cryptography, which combines traditional encryption methods with quantum-resistant algorithms such as ML-KEM. This model allows organizations to strengthen their security posture without immediately replacing existing cryptographic systems. By running classical and quantum-safe encryption simultaneously, hybrid cryptography provides a smooth transition toward quantum-resilient security while maintaining compatibility with current infrastructure.
Preparing for the quantum era also requires organizations to adopt a strategic security framework. Key steps include identifying sensitive data that must remain protected for many years, mapping where encryption is used across systems, and beginning the transition to hybrid cryptographic models. Security teams must also maintain visibility into the cryptographic algorithms used in their networks and ensure compliance with evolving regulatory standards.
Equally important is the role of Zero Trust security architectures, which enable organizations to inspect encrypted traffic and enforce security policies even as encryption technologies evolve. By integrating post-quantum cryptography with Zero Trust frameworks, enterprises can maintain visibility and control across their networks while safeguarding sensitive information against future threats.
As quantum computing continues to progress, the cybersecurity landscape will inevitably change. Organizations that begin preparing now by exploring post-quantum cryptography strategies will be far better positioned to protect their critical data and maintain resilience in the coming quantum era.
See What’s Next in Tech With the Fast Forward Newsletter
Tweets From @varindiamag
Nothing to see here - yet
When they Tweet, their Tweets will show up here.